Are you looking for more privacy online? With so many prying eyes on the Internet, this is a tough task, but luckily, there are several tools that you can use to improve your privacy online.
You probably heard of the two most important online privacy tools that you can use – Tor and VPN. But which one is better? After all, they overlap in many things.
Well, why debate at all whether Tor is better than VPN or vice versa when you can use VPN and get more privacy that way?
In this article, we’ll show you how Tor, or Onion VPN works and why it’s a good idea to combine the two.
First, though, let’s see what Tor and VPN are individually and how they work to make your online traffic more secure, private and anonymous.
What is Tor?

Tor, or The onion router, is a free, open-source software program originally developed by the United States Navy, that can protect online users against Internet surveillance and traffic analysis.
To use the Tor browser you first need to download the software from the Tor Project webpage for your OS (Windows, OSX, Linux or, Android) and install it on your computer.
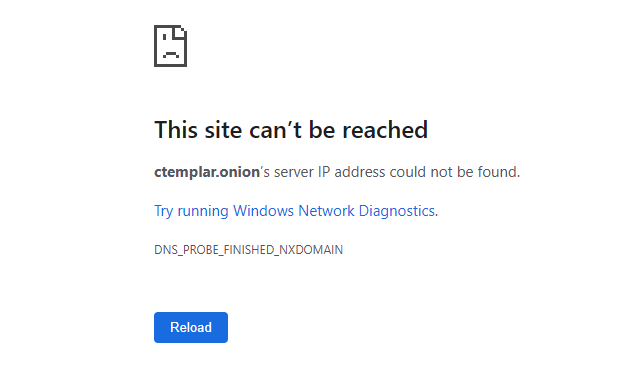
Only then will you be able to access websites on the Tor network as they all use a .onion domain instead of the “regular .com, .org, or .net. If you try to access a .onion site via a normal web browser like Chrome or Safari, you’d only get an error message like this:
However, once you have Tor installed and configured you’ll be able to browse online with more security against malware and online tracking than before as Tor routes the traffic via “nodes”, hiding your real location and identity.
What is a VPN?
Another widely used online privacy tool is a Virtual Private Network, or VPN.
VPN allows you to surf the Internet anonymously by masking your IP (Internet Protocol) address and replacing it instead with that of the VPN server.
So for instance, if you are accessing a website from France, the website admin will be able to see this thanks to your IP. However, if you are using a VPN server in, let’s say, Laos, it will now show an IP in Laos.
This is all done through tunneling and encrypting your online traffic, allowing you to not only hide your real IP, but also your web activity, browsing history, streaming location and device you use.
Why Use Onion over VPN?
Both Tor and VPN are useful tools, but have their own flaws.
However, we are not here to compare Tor vs VPN, but rather to show you why you should use Onion over VPN for better privacy and anonymity.
Using Onion over VPN allows you to utilize the best of the two and in many ways hide their individual deficiencies. This provides the anonymity of Tor (read this article to learn how far Tor anonymity goes), plus the privacy of the VPN.
One of the reasons to use Tor over VPN is that using Tor alone might in some countries cause you problems and mark you as a criminal (or at the very least someone of “interest”).
Your ISP would be able to see that you are connected to Tor. By using a VPN, you encrypt the data before and after it gets to the Tor entry node and hide your IP address. If the entry node is compromised in any way, then the anonymity that Tor normally provides is gone.
As such, it becomes more difficult for someone to discover that you are using the Tor network.
In short, here are the advantages of using Onion over VPN:
- Your ISP can’t see that you are connected to Tor. Instead, it will see your VPN connection, with Tor concealed. While some websites block VPN access, you’ll still encounter far fewer problems of that nature than with Tor alone;
- Exceptionally strong end-to-end encryption. Tor over VPN provides multiple layers of encryption;
- The Tor entry node can’t see your real IP address. Instead, it will only see the IP of the VPN server;
- The VPN will only see that you’re connected to the entry node. It won’t be able to see your traffic through the Tor network.
That said, there are a few disadvantages that bear mention. In particular:
- Do you trust the VPN provider? While your ISP will no longer be able to see your true IP address, the VPN provider will;
- Your Tor traffic could become exposed to the ISP if the VPN connection drops or if it has a DNS leak. To prevent this from happening, make sure that the VPN you are using has a kill switch.
How to Use Tor over VPN?
Onion over VPN connection looks like this:
User > VPN Server > Tor Network > Destination.
Using Tor over VPN sounds complicated, but it’s really not. It’s just a matter of not skipping any steps.
- Sign up for a VPN service. A good option is NordVPN.. You might also want to cover your tracks more by using anonymous payment if the option is available (it really should be);
- Once you complete the payment, download and install the VPN client on your computer. This is a simple procedure just like installing any other software;
- Next, find a suitable VPN server and connect to it. Look for servers that give you the best speed;
- Go to the Tor Project page and download the Tor client for your operating system;
- Install the Tor browser on your device. If you’re not sure how to do this, follow this guide;
- Launch the Tor browser. You can now connect to the Tor network.
To make things even easier, some VPN providers like NordVPN already have a built-in Onion over VPN feature, allowing you to browse anonymously without all the configuration hustle.
Why Not VPN over Tor?
You could also go the other way and use VPN over Tor. However, Onion over VPN is a better and easier-to-configure option.
The only “benefit” of this method is that it will provide you more privacy from the VPN provider as it now won’t be able to see your real IP address. However, if you already don’t trust them, why use them at all?
On the flip side, your Internet speed and performance will suffer greatly and you’ll only be able to access .onion hidden websites on the Tor network, while with Onion over VPN you can access any website on the Internet.
Finally, it is also mentioning that neither Tor nor most VPNs recommend or allow this kind of setup.
Double VPN vs Onion over VPN
What about using a VPN on another VPN, or “double VPN”? Would this be a good idea and how Double VPN vs Onion over VPN compares?
To use VPN over VPN, you will need to:
- Install a Virtual Machine (VM) on your device;
- Next, install the VPN on both your computer and your VM. Keep in mind that this will count as two devices, so make sure it won’t go over the maximum number of devices your VPN provider allows. NordVPN for instance supports up to six different devices;
- Launch the VPN as you normally would and select a server to connect to;
- Turn on the VM and launch the VPN on it as well. Choose a different server from the first one.
Onion over VPN vs Double VPN is similar in some ways, but there are important differences to keep in mind.
With Tor over VPN, your Internet traffic is first encrypted by the VPN. From here, it goes through several encryption layers, before going through the Tor network and its nodes.
On the other hand, with a VPN on VPN the first VPN server encrypts your traffic, which is then routed to the second VPN, which decrypts the traffic and then re-encrypts it before it goes through the tunnel to the desired website.
It is also worth noting that very few VPNs support Double VPN. This is because the provider would need an extra system that would allow them to track the user activity on such connection, while keeping the data encrypted to 3rd parties if they are to maintain the “no-log” policy.
How to use Onion over VPN?
To use Onion or Tor over VPN:
- Sign up for a VPN service;
- Download and install the VPN on your computer;
- Turn on the VPN;
- Download and install Tor browser;
- Launch Tor.
What does Onion over VPN mean?
Onion over VPN allows you to route your traffic through a VPN server first and then pass it through the Tor Network before it reaches the desired destination on the Internet (the website you want to visit).
Conclusion
Privacy, anonymity and security on the Internet are all important, but are in short supply and we have to constantly fight for them. Onion over VPN is possibly the best way to get the best out of both Tor and the VPN and keep prying eyes, including your ISP away from your traffic and data.
Do you want to protect your email privacy as well? Sign up to CTemplar and create your anonymous encrypted email today.