Today, we are far from lacking in online communication options. The Internet provides us with multiple ways to connect with other people all around the world, including Skype, Slack, Google Hangouts, online forums, Twitter, Discord and so on.
However, with over 4 billion users, email is still the number one means of communication, especially in business settings, where an average office worker receives 120 emails per day, according to Campaign Monitor.
Not all these emails will be equal though. Some estimates are that at least every 5 out of 10 emails you receive will be spam. Of the remaining emails, there’s a good chance that they might contain some sensitive information that you don’t want the wrong person to get their hands on.
How do you prevent that from happening?
By using email encryption. One type of encryption and the one that I want to cover here is the PGP email encryption.
What is Online PGP Encryption?
PGP or Pretty Good Privacy is one of the most popular encryption systems around and it dates back to 1991.
Originally, PGP encryption was freeware, which allowed it to spread fast and gain popularity. However, on April 29, 2010, Symantec acquired PGP Corporation in a $300 million deal and soon made PGP a proprietary software.
However, in 1997, PGP Inc proposed a standard called OpenPGP to the IETF, which the latter accepted and started the OpenPGP Working Group.
Since the two are practically the same (OpenPGP was just created to eliminate some licensing issues outside the US), I’ll mostly talk about PGP here.
PGP is a combination of two encryption standards: symmetric and asymetric. That way, PGP can take the best out of both, namely the security of asymmetric, public-key cryptography and the efficiency of symmetric encryption.
Alone, symmetric encryption wouldn’t be secure enough as both the sender and the recipient would have the same key and the sender would have to share this key in an insecure plain text. On the other hand, asymmetric cryptography is much slower.
How Does PGP Work?
So how does the PGP encryption algorithm work?
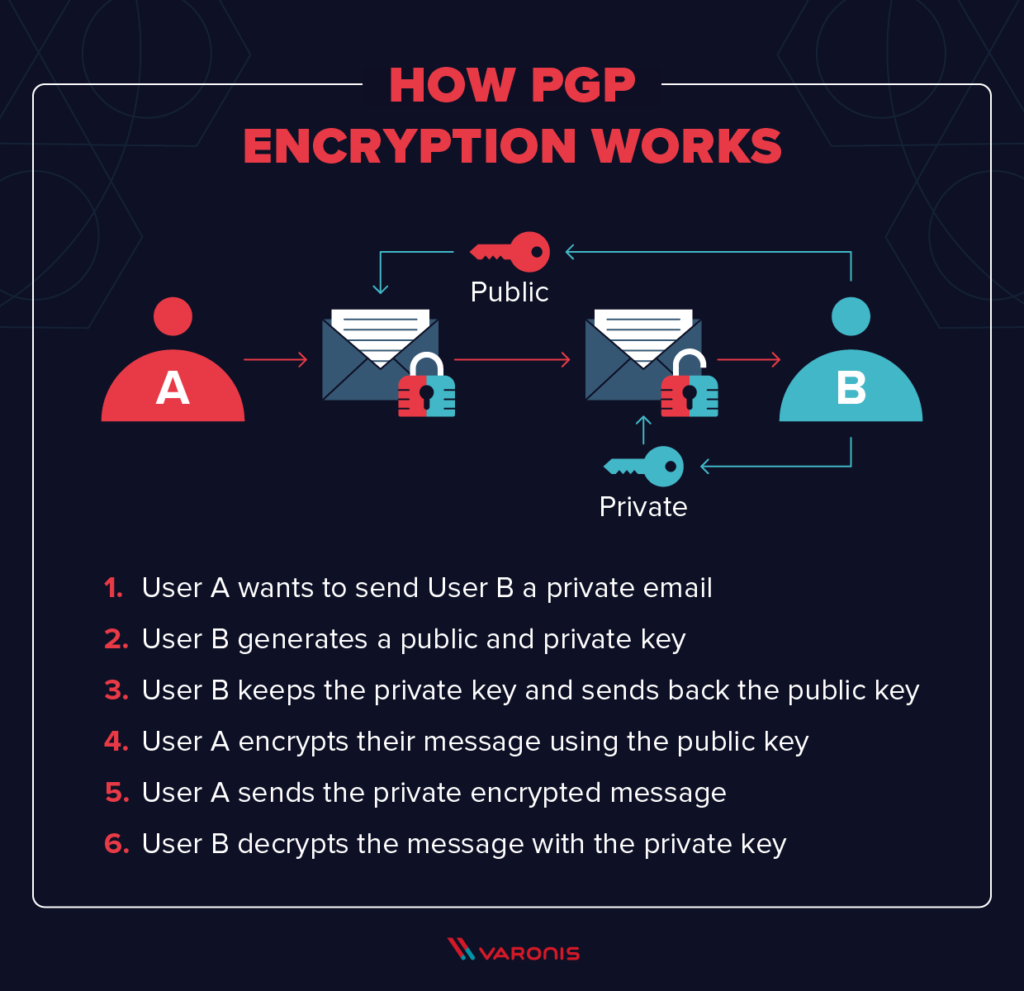
Here’s an example of PGP in action:
- Let’s say Sara wants to send Jane a private email and she doesn’t want their boss Bill to see it;
- Jane now needs to generate two keys. One public and one private;
- She now shares the public key with Sara, but she keeps her private key. Think about the public key as the PO box, where everyone can now the location, but they only you would be able to open it with your private key;
- Next, Sara uses the public key that Jane shared with her to encrypt their message;
- Now she can send a private encrypted message to Jane;
- Finally, Jane uses her private key to decrypt the message between her and Sara and their boss Bill is unable to read it, even if he has the public key.
What are the Benefits of PGP Encryption Email?
Do you need to encrypt your emails with PGP?
Not necessarily. Some other standards might work better for you. However, PGP encryption brings an array of benefits, including:
- Ability to share information with others (including individuals AND groups) in a secure manner;
- Emails secured with PGP encryption cannot be infected by email attacks or penetrated;
- The software is very easy to learn and use and requires very little training;
- PGP also verifies the sender, ensuring that the email was not intercepted and modified by a hacker;
- The private key ensures that the information encrypted with it can’t be viewed, stolen or changed by hackers without your knowledge;
- Once you delete them, sensitive information cannot be recovered by hackers. Read about how to instantly delete your emails once you send them on CTemplar here.
Are There any Limitations to PGP?
Of course, no encryption standard is perfect and PGP is no exception.
One of the major disadvantages of PGP is that it is not anonymous by default as it won’t encrypt every part of the email, but only the body. Meanwhile, the information about the sender and the recipient, as well as the subject line will remain unencrypted.
For instance, if Sam wants to send an encrypted message to Lana, but wants to keep his name hidden, PGP alone won’t allow him to do that.
Instead, he would need to use a secure email service like CTemplar, which also uses the OpenPGP.js library.
What are the Uses of PGP Encryption?
- Encrypting emails;
- Verify the identity of the sender;
- Encrypt files at rest.
The most common use of PGP is to encrypt emails that you send and receive.
However, PGP has two other main uses.
One of them is to verify the sender’s identity. Let’s say Mandy has received an email that claims it’s from her mother. Using PGP Digital Signature, Mandy can verify if it was her mother or someone else who sends this message.
Another (third) use of PGP is to encrypt files. PGP encryption algorithm is, for all purposes, unbreakable. This makes it a very secure way to encrypt files at rest.
Do You Need a 3rd Party Software to Run PGP Encryption?
It used to be that, to use PGP software, you had to download an add-on for your email client and install it.
For instance, if you are using Gmail, you need to download either FlowCrypt or Mailvelope.
Once the app is downloaded, an app permission prompt will pop up. Hit the “Add” button to accept.
This opens a new browser tab in which you need to click on the button in the top right corner to configure this addon.
Click on the lock icon opens a configuration menu. From here, you can choose between Import Key (if you already have a PGP key) or, Generate Key (if you don’t have a key, which is more likely).
Once the key is generated, a new page will open where you can enter the Mailvelope key registry full name and your Gmail address and password. Once you’ve added these details, you will get a “Success! New key generated and imported into keyring” message.
PGP add-ons are available not just for Gmail, but also for Apple Mail, Microsoft’s Outlook and Thunderbird.
However, with installing a 3rd-party app like this, there’s always some chance for PGP to be wrongly configured.
Because of this, it’s safer to use a secure email system that already includes PGP by default, such as CTemplar.